Email phishing scams
Phishing is when someone tries to get personal information (like bank account numbers and passwords), from a large audience, so they can use it to impersonate or defraud people. These emails can look very real, and some will even use the branding and logos of a legitimate organisation to make the email seem genuine. Phishing…
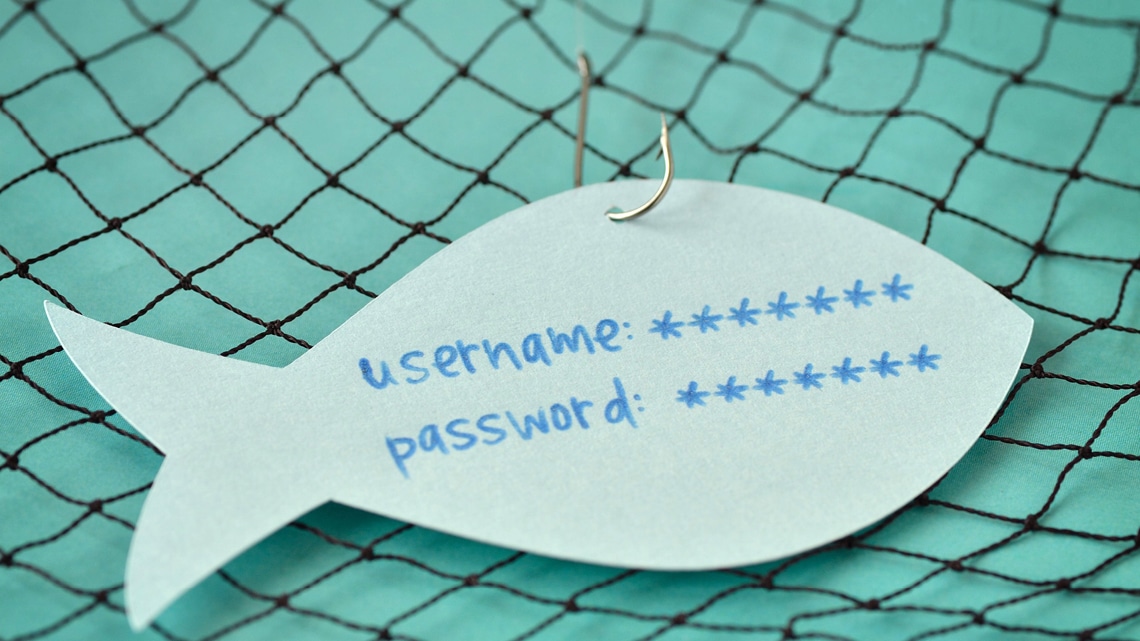
Phishing is when someone tries to get personal information (like bank account numbers and passwords), from a large audience, so they can use it to impersonate or defraud people. These emails can look very real, and some will even use the branding and logos of a legitimate organisation to make the email seem genuine.
Phishing scammmers will contact a large number of people in the hope that some of them will fall for the scam. These scams can seem like they’re being sent just to you, but in reality the same scam is being sent to hundreds, if not thousands of people at the same time.
Phishing scammers will often claim to be from a legitimate organisation, or to have some kind of ‘deal’ to be claimed. For example, a scammer may send out an email telling people they have won a lottery, and to claim the winnings they need to provide some details. Other phishing scams use scare tactics, where the scammers pretend to be lawyers or employees of the government and threaten legal action if you don’t give them information or money. We’ve also heard of scam emails claiming that online accounts or memberships have been cancelled, have expired or have details that need updating.
How does phishing work?
Phishing attempts often look or sound genuine because the scammer is impersonating a trusted organisation or person. They could be pretending to be from your phone or internet company, a law firm, your bank or even the government. The scammer asks you to update your details, provide details, complete a survey, make a payment or another request that gives them access to your personal information.
Are there other types of phishing?
There are other types of phishing scams including:
Spear phishing: spear phishing is the same as regular phishing, but there is some reason why the people contacted have been targeted.
Whaling: whaling is a type of phishing scam that is highly targeted to a certain person that the scammers can gain a lot from – for example, high-level business people, politicians and celebrities.
Are phishing emails obvious?
The short answer is no. Some phishing attempts look obvious, while others don’t. Phishing scams are becoming more difficult to spot as scammers become more sophisticated. There are some basic rules to follow to help keep yourself safe online in the Email Phishing 101 Guide, and if you’re still unsure if an email is legitimate you can contact us for advice.
How can I protect myself?
- Be cautious about emails asking you to update or verify your details online
- Be cautious of emails saying you’ve won prizes from competitions that you don’t remember entering
- Be cautious of emails that try to get you to act quickly by threatening you with legal action or loss of an account
- Ignore any emails asking you to provide personal information like passwords, or banking information
- Remember legitimate organisations like banks will never ask you to send them your password
- Only open email attachments when you’re expecting them, even if you know who the sender is
- If you’re unsure if an email is from a legitimate organisation, you can contact them to ask. If you do contact them, make sure you go through their official contact channels – don’t use the phone numbers, websites or email addresses included in the email
- You can also try an internet search using the names or exact wording of the email to check for any references to a scam – many scams can be identified this way
- If you’re still unsure if an email is legitimate you can contact us for advice
What to do if you’ve received a phishing email
If you receive a phishing email, do not reply to it.
- You should mark the phishing email as junk mail. When an email is marked as junk mail, your email filter will learn to redirect emails from that scammers email address away from your inbox.
- If you’ve clicked through any links or attachments that were included with a suspicious email, our advice is to check for malware (malware is malicious software such as viruses) on the device you were using at the time. You can use a free online scanner to look for threats on your computers.As an independent non-profit, Netsafe can’t recommend a particular product but we have listed some options here from well-known, reputable companies.For PC: ESET online scanner or Kaspersky Virus Removal Tool. After this scan has been completed, you can run Malwarebytes Anti-Malware free edition.
For Mac: Bitdefender Antivirus for MAC or ESET Cyber Security for Mac or AVG Antivirus for Mac are also good alternatives. - If you provided any sensitive personal information or security related information such as your mother’s maiden name, and/or former residential address or bank account details, you should contact your bank immediately. It’s important that you explain the situation to them in full and give the bank the opportunity to decide on the security process to follow.
- Use this Identity Theft Checklist as a helpful guide on what could happen with the information you provided. If you believe you were exposed to identity theft, we recommend you contact iDCare as they provide free help and support for New Zealanders.
- If the scammer is pretending to be from a legitimate brand you can forward it to that organisation so they know about it.
- Westpac [email protected]
- TSB [email protected]
- TradeMe [email protected]
- PayPal [email protected]
- Kiwibank [email protected]
- IRD [email protected]
- BNZ [email protected]
- ASB [email protected]
- Apple [email protected]
- ANZ [email protected]
- Countdown: [email protected]
- Waka Kotahi (NZTA): [email protected]
Report a scam
Help if you have been scammed or think you are about to be scammed: Netsafe can’t open investigations or track scammers, but we can offer support and advice for people who have lost money in a scam, or think they are about to. You can report a scam to www.netsafe.org.nz/report.
More information
- More information on scams
- Quick guide for staying safe online
- Online safety advice for parents
- Online safety advice for businesses
Keep up to date
Follow us on social media and sign up to our enewsletter for alerts, news and tips.